
Phishing Techniques: Understanding and Preventing Cyber Threats
One of the most prevalent and dangerous online threats currently in the online environment is phishing, which targets individuals, businesses, and even government agencies. At its core, it is a phishing technique used by hackers and cybercriminals to deceive people into handing over sensitive data such as passwords, banking credentials, credit card numbers, or personal identification details. This trick makes phishing particularly successful because it looks real. These attacks can appear fully legitimate, created to resemble trusted companies, service providers and banks. Due to this engaging look, victims often end up getting into this trap without even knowing that something is missing until it is too late.
Phishing techniques are diverse. Some are fake websites that are designed to look like the actual websites with almost perfect precision, and others are based on fraudulent emails, text messages, or even voice calls. The result is always the same in all of these cases: to fool the victim into clicking, sharing, or disclosing information that can be stolen and abused. This stolen information is sold on the dark web, is used to commit identity theft, or is used to execute bigger cyberattacks that affect whole organizations.
Nearly 1.2% of all emails sent are malicious, which in numbers translates to 3.4 billion phishing emails daily. – Astra Security Report 2025
As phishing continues to evolve, so do the phishing methods and techniques that attackers employ. Other campaigns are general and wide-ranging, sending spam emails to millions of users simultaneously, hoping that a small percentage of them will reply. Some are extremely specific and customized and are specifically tailored to defraud an individual or business executive. These more sophisticated types of phishing tend to rely on social engineering, leveraging personal information obtained via social media or professional networks to establish trust and then attack.
The most important step in developing effective defenses is to understand the various kinds of phishing. Through understanding the way phishers think and work, people can identify warning signs before clicking on a harmful link, and companies can teach their employees to be wary of suspicious messages. Being aware of the red flags – the changes in email address as minor as they might be, the demands to share confidential information as urgent as it might seem – will help individuals to keep one step ahead. When individuals and organizations integrate awareness and technical safeguards, they stand a great chance of not becoming victims of these ever-changing cyber threats.
Table of Contents

What is Phishing and Phisher Meaning
Phishing is a criminal activity that involves the use of the Internet to impersonate an authoritative person, a company, or an organization to defraud them into providing sensitive data. Such a deception may happen in a variety of ways: in the form of emails written in a very clever way, in the form of text messages with malicious links, in the form of fraudulent telephone calls, or in the form of fake websites that may resemble the real ones to the letter. The motive is always the same: to gather personal information like usernames, passwords, credit card details, or government-issued identification numbers. After the attackers have access to this data, they can use it in many different ways, such as identity theft, emptying bank accounts, unauthorized purchases, or hacking into corporate systems to commit larger-scale fraud.
According to the IBM Cost of a Data Breach Report 2024, it is revealed that an estimated $4.88M per phishing breach, social engineers are making billions by being better at making people click than we are at understanding what makes them tick.
Such an attacker is referred to as a phisher. The meaning of phisher is simple: it is the cybercriminal who organizes such tricks. But the techniques phishers employ are not easy. Depending on the nature of the attack, they may masquerade as banks, online sellers, service providers or even co-workers. Examples include being sent an email purportedly by your bank requesting that you confirm your account details, or getting a phone call purportedly by tech support that you have been the victim of an actual security breach. In both scenarios, the phisher exploits two psychological appeals, which are trust and urgency. They make victims act without second thoughts by seeming to be a trustworthy figure of authority and by instilling a feeling of imminent threat.
The first step in countering these threats is to understand the nature of a phisher and their operation. It is not only about the identification of bad grammar or suspicious links; nowadays, phishing attacks are highly advanced and can be almost indistinguishable between real and fake messages. You can make yourself significantly less vulnerable by training yourself to stop and think before clicking links, to verify sender information, and to check requests using official channels. Knowledge of the role of the phisher in such schemes will enable individuals and businesses to detect, prevent, and report phishing activities before important data is lost to the wrong hands.
Types of Phishing and Forms of Phishing
Phishing is not a single type of cybercrime, but rather a subdivision of it, which is tailored to different vulnerabilities. Some of the common forms of phishing are spear phishing, email phishing, vishing, and smishing. All these approaches aim at users in different ways, including the personalization of attacks to a single user and the sending of bulk spam messages to thousands of users.
The forms of phishing vary not only in delivery but also in sophistication. Others are mere scams that have spelling mistakes, and others are highly sophisticated spoofing techniques that can recreate a valid site or email address with terrifying effectiveness. These categories of phishing will help cybersecurity experts to be better prepared to protect against them and educate users to be able to identify red flags before becoming a victim.

Spear Phishing: Targeted and Personalized Cyber Attacks
Spear phishing is very focused, unlike traditional phishing campaigns, which reach a large number of individuals. In this case, the attackers study their target in advance, frequently via social media or business social networks such as LinkedIn. This enables them to develop very persuasive messages that seem personal and credible. This sophisticated phishing method represents one of the most dangerous forms of targeted cybercrime.
The threat of spear phishing is its accuracy. The email that the victims get might seem to be sent by a colleague, boss, or a trusted partner requesting the victim to open a link or provide sensitive information. It is more difficult to detect as a scam because it is personal. Businesses are especially vulnerable to spear phishing since a single compromised employee account can be used to facilitate a massive breach.

Email and Spam Phishing: The Most Common Form of Attack
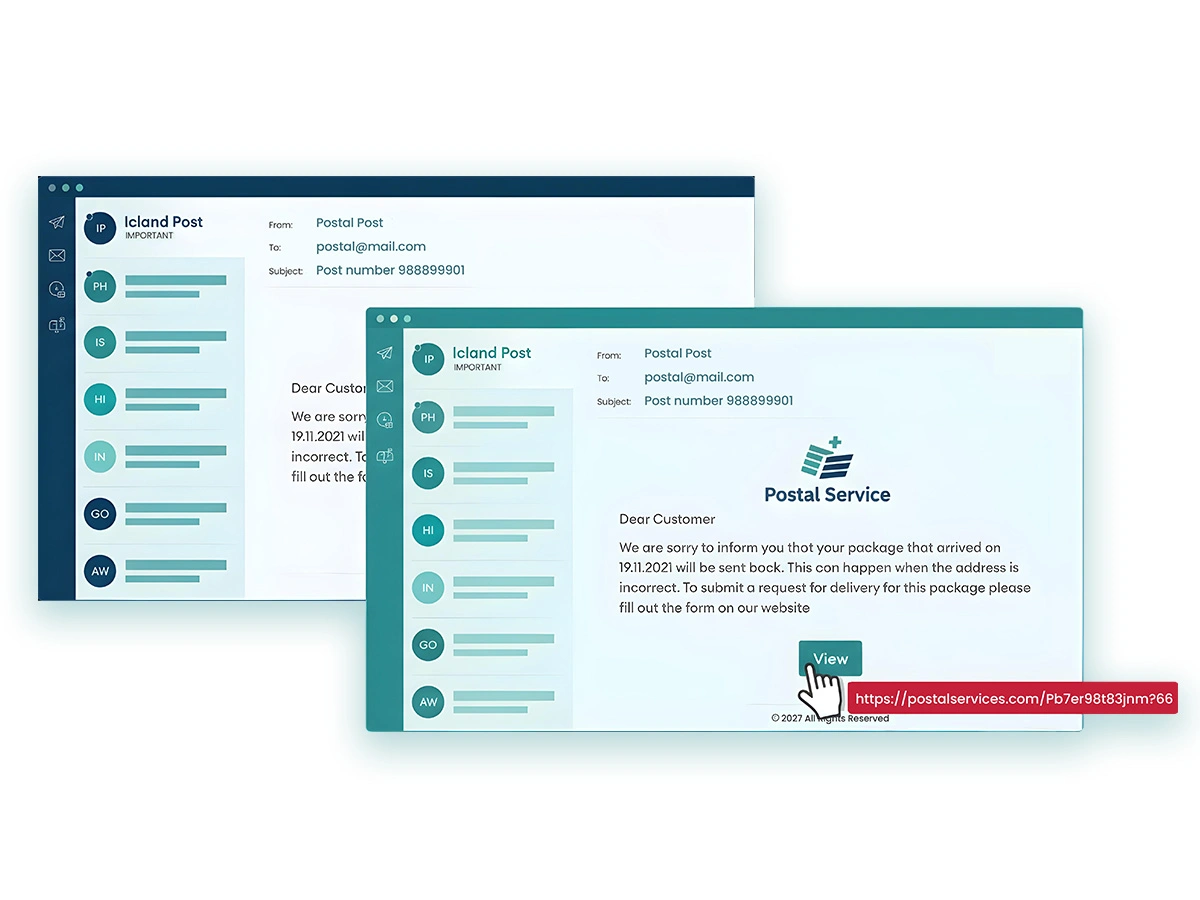
The most common phishing technique is email phishing. Attackers use bulk spam mail messages that appear to be official messages of a bank, online service or a government agency. Such emails usually have harmful links or attachments that steal information or infect the computer of the victim.
The most common phishing technique is email phishing. Attackers use bulk spam mail messages that appear to be official messages of a bank, online service or a government agency. Such emails usually have harmful links or attachments that steal information or infect the computer of the victim.
The most common phishing technique is email phishing. Attackers use bulk spam mail messages that appear to be official messages of a bank, online service or a government agency. Such emails usually have harmful links or attachments that steal information or infect the computer of the victim.
Web-Based Delivery Phishing
The other type of phishing that is commonly used in cyber security is fraudulent websites. Attackers generate web pages that resemble legitimate web pages, like an online banking portal or e-commerce site, and send the victims links to those web pages. As soon as the victim types in their login details, the attackers steal the data immediately.
This type of phishing may be particularly harmful as counterfeit websites look almost like the original ones. In-session phishing and other tricks allow users to be compromised without even knowing it until their accounts are abused. Risk reduction can be achieved by learning how to check the URLs of websites and by utilizing multi-factor authentication.
Organizations need to ensure their legitimate websites are properly secured through professional Website Design & Development Services that implement the latest security protocols and SSL certificates.

Link Manipulation: How Cybercriminals Trick Users into Clicking
Link manipulation is one of the most misleading phishing tricks. The attackers camouflage malicious links in the emails, social media posts, or text messages to attract users to click. Such links are usually valid, but they might contain minor modifications, such as an additional letter in a URL, which one does not notice.
“URL manipulation attacks have increased by 220% in 2024, with attackers using domain spoofing and typosquatting to deceive users.” – Cybersecurity & Infrastructure Security Agency (CISA)
The link manipulation definition means that one changes the apparent text of a link to seem harmless but to take one to a harmful destination. As an example, a phisher can construct a URL such as paypa1.com rather than paypal.com. When the user clicks the link it will be redirected to the fake login page or a website that installs malware and virus automatically. Proper information and guide to beware from such links is really important.

Session Hijacking: Exploiting Web Sessions to Steal Data
In session phishing, also known as session hijacking, is the process in which an attacker stealing a user’s active session cookies from a known website. Whenever the user logged in, they are assigned a session ID that identifies them. When the hackers get access to this session ID, they can impersonate the user and access sensitive information.
This form of phishing is especially harmful because the victim might not suspect anything. On company’s scale, it may imply hacking into customer accounts, payment systems, or company data. Strong encryption, secure session management, and detection of suspicious activities during browsing are needed to protect against session hijacking.

Content Injection: Altering Trusted Pages for Phishing Gains
One of the more sophisticated phishing methods in cybersecurity is known as content injection, where the attacker modifies the content of a legitimate website to deceive users. Rather than creating a rogue site, cybercriminals use the vulnerabilities of an existing trusted site to place malicious forms, pop-ups or links.
As an example, a phisher can hack into a banking site and insert a bogus login form. Users are tricked into putting in their credentials, thinking they are on the actual site, as attackers gather the information. This complicates the process of detection since the users are communicating with a real domain. Protection from content injection requires regular features updates, strong firewall security and virus scans.

Phishing Through Search Engines: Fake Sites and SEO Manipulation
This is a lesser known type of attack by using search engines. In such an attack, criminals build deceptive websites that look like authentic services such as government websites, payment gateways, or online shopping websites, and then apply search engine optimization techniques to ensure that the fake websites appear at the top of the search results.
Both victims who are looking to pay their taxes or renew their driver’s license could accidentally visit such fraud sites by typing in the words tax payment portal or driver license renewal. After arriving there, they can be requested to give personal data or pay directly to attackers. This method emphasizes the need to check URLs themselves and not to trust search results only because of their position in the ranking.
Understanding legitimate SEO Services and how they work can help users recognize when websites are using manipulative tactics to rank higher in search results for malicious purposes.

Vishing (Voice Phishing): Phone-Based Social Engineering Attacks
Phishing or vishing via telephone is a type of attack where malicious individuals make phone calls to their victims, impersonating trusted parties. They can pretend to be a bank, government agency, or tech support team. Attackers can use a sense of urgency to make victims disclose sensitive information by making statements such as your account will be frozen unless you verify your information.
“In the first quarter of 2024 alone, nearly 964,000 phishing attacks were recorded, with a notable rise in voice phishing, or ‘vishing.'” – SOCRadar Cyber Intelligence
The phishing technique over the phone has become more sophisticated with robocalls, caller ID spoofing, and AI-generated voice technology. Until unauthorized transactions are made, victims are not aware that they have been scammed. The risk of this particular phishing can be lowered down with frequent training of employees and educating the individuals to check only the official channels for information.
SMS Phishing Method: Text Message Scams Targeting Users
Smishing is a phishing technique that exploits SMS or messaging applications to deceive users. The victims are sent a text containing a malicious link, which is usually hidden as an emergency alert, such as: Your package delivery failed, click here to reschedule, or Your account has been locked, verify now.
Smishing works remarkably well because individuals tend to believe brief text messages. When these links are clicked, they can be malware downloads or spoofed logins. To prevent such attacks, you need to be aware of them and avoid such suspicious links in the text and specially when people send them through catchy tactics.
Companies that apply valid SMS marketing strategies must apply adequate authentication and protection to ensure that their brands are not spoofed in smishing attacks.
FAQs
The red flags to be considered are bad grammar, unknown sender addresses, urgent or threatening messages and links that do not belong to the official domain. Move the cursor on links and then click to obtain the actual URL. In any case of uncertainty, contact the sender through the official channel.
Disconnect to the Internet, do not open any other links and scan the computer with malware. Always change passwords immediately and report to your bank or IT department in case of sharing sensitive information. Quick reaction minimizes damage due to a phishing attack. In the case of businesses, a detailed digital marketing strategy, which involves security awareness training, can aid in avoiding the cases when employees fall prey to phishing attacks.
Yes. Corporations become vulnerable to spear phishing, CEO fraud, and BEC (Business Email Compromise) fraud on financial transactions and confidential information. Individuals will be more susceptible to email spam, smishing and vishing. Both groups need awareness and prevention measures.
Good first lines of defense are firewalls, email filters, anti-virus software and browser security add-ons. High-tech devices are AI-based anomaly detection systems that detect abnormal patterns of communication and reduce the possibility of phishing and hacking attacks. The organizations should also think of adopting the safe search practices and getting to know the best private search engines that are more concerned about the privacy and security of the users.
Conclusion
Phishing is one of the most persistent and flexible cybersecurity threats. Attackers are continuously improving their techniques, starting with link manipulation and session hijacking, phishing via the phone, and smishing. The secret to avoiding this is to know these evolving strategies.
People and companies need to adopt a multi-layered defense strategy. This will entail user education, good authentication, technical security and ongoing monitoring. Having known the various forms of phishing attacks, the detection of such attacks, and the proactive steps we can take to avert the risks and secure our online lives to a large extent.
To ensure that businesses have a secure online presence, it is advisable to have a complete security system in place with professional Website Development services that focus on cybersecurity at the very bottom. Also, a good Online Reputation Management strategy can assist in ensuring that your brand is not impersonated in phishing attacks.
Knowing about threats such as ransomware and being aware of many cybersecurity threats will make you develop a more holistic defense against any type of cybercrime.
ITVerticals Services

Top 10 SEM/PPC Strategies for Better ROI in 2026

Mobile App Development Cost: What You Need to Know in 2026

Top 10 Instagram marketing strategies that work in 2026

Phishing Techniques: Understanding and Preventing Cyber Threats

How to Create a Landing Page That Actually Converts in 2026
Top 10 SEM/PPC Strategies for Better ROI in 2026

Mobile App Development Cost: What You Need to Know in 2026

Top 10 Instagram marketing strategies that work in 2026

